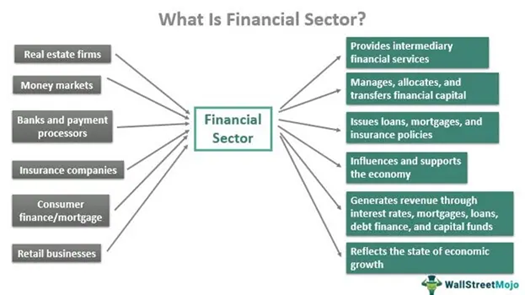
It is no wonder that the Financial Sector remains one of the most prominent targets for cyber-attacks. Most cybercrimes are committed for financial gain. Hence, financial institutions have to be extra cautious and ensure they have robust cybersecurity technologies and measures to thwart cyber threats and minimize risks.
Before we delve deeper into the cybersecurity measures and solutions for the financial sector, let us understand the ongoing trends.
Notable Trends in the Financial Sector

Digital Banking: With everything going digital in this era, consumers resort to smartphones and computers to manage their finances and conduct transactions. The need to visit bank branches has been reduced drastically.
Fintech: As the name suggests, companies use technology to provide innovative financial services like mobile banking apps, payment apps, lending platforms, investment apps, etc. It contributes extensively to the convenience of consumers and businesses in new ways.
Open Banking: Open banking allows consumers and businesses to share their financial data with third-party providers. For instance, a digital payment app like PayPal or Gpay requires access to your financial data to proceed with online payments. Similarly, third-party platforms for lending, investment, or account aggregation require access to financial data. Open banking is growing popular with more products and services entering the market.
Cryptocurrency: Cryptocurrency is a digital or virtual currency that uses cryptography for security. Cryptocurrency is becoming increasingly popular, and financial institutions are beginning to offer products and services related to cryptocurrency.
AI and ML: Financial institutions have started using Artificial Intelligence (AI) and Machine Learning (ML) to personalize financial advice and automate processes.
Cybersecurity: Despite several advantages, digitalization expands the cyber threat landscape, calling for investment in cybersecurity to protect customers and their assets.
Cyber Threats Targeting the Financial Sector

Phishing attacks: Cybercriminals design emails and websites emulating those of legitimate financial institutions and trick users into revealing sensitive information like passwords or credit card numbers.
Malware attacks: Malware can be injected through phishing emails, attachments, or infected websites. They are used to steal data or disrupt financial operations by taking down websites, ATMs, and other systems, causing financial losses and inconvenience to customers.
Ransomware attacks: After gaining unauthorized access, cybercriminals encrypt critical data or systems of financial institutions and demand a ransom to decrypt them. Ransomware attacks cause financial losses and reputational damage due to inadequate security measures.
Denial-of-service (DoS) attacks: DDoS attacks overwhelm a system with traffic, making it unavailable to legitimate users. With many users and businesses resorting to digital banking, DDoS attacks can severely hamper financial services and cause financial losses.
Supply chain attacks: Financial institutions rely on third-party services for software, hardware, and professional services. When cyber attackers identify vulnerabilities and compromise third-party hardware or software, they can easily gain access to financial institutions’ systems and initiate malicious activities like data theft or ransomware attacks.
Poor Security Practices of Customers: When customers engage in poor security practices, it can make it easier for attackers to target financial institutions. Using weak passwords, clicking on malicious links, downloading attachments without verifying the source, and sharing sensitive information like credentials or credit card numbers are the poor practices users indulge in without cyber awareness.
ATM Jackpotting: Cybercriminals exploit the vulnerabilities of ATM software or hardware to steal large sums of money.
Identity theft & Account Takeovers: Cybercriminals steal personal information to impersonate victims and gain unauthorized access to financial accounts. Using compromised accounts, they commit fraudulent activities and pose serious threats to the financial security and privacy of the account holders.
Investment & Cryptocurrency Scams: Investment & Cryptocurrency Scams lure investors with false promises of high returns. Investment scams target various investors, while cryptocurrency scams focus on those interested in digital currencies. In both cases, cybercriminals engage in fraudulent schemes.
Common Security Regulations for Financial Institutions

Gramm-Leach-Bliley Act (GLBA): GLBA is a US law that requires financial institutions to protect customer data and to disclose their data-sharing practices.
Payment Card Industry Data Security Standard (PCI DSS): PCI DSS is a global standard for protecting payment card data. It is a must for all organizations that accept, process, or store payment card data.
Sarbanes-Oxley Act (SOX): SOX is a US law that requires public companies to maintain accurate financial records and to implement internal controls to prevent fraud.
General Data Protection Regulation (GDPR): GDPR is a European Union regulation that gives individuals control over their data. It applies to all organizations that process personal data of EU residents, regardless of where the organization is located.
ISO/IEC 27001: ISO/IEC 27001 is an international standard for information security management. It provides a framework for organizations to manage their information security risks.
Cybersecurity Measures To Mitigate Cyber Risks

Implement a layered security architecture. A layered security architecture involves multiple security controls like firewalls, Intrusion Detection Systems (IDS), antivirus software, and data encryption to protect systems and data.
Educate employees on best cybersecurity practices. Employees are frequently the most vulnerable point in cybersecurity. Therefore, train them on security practices like recognizing phishing emails and making strong passwords.
Have an Incident Response Plan. It is important to have a plan in place for responding to incidents. This plan should include steps for identifying, containing, and eliminating threats, as well as steps for communicating with customers and other stakeholders.
Cybersecurity – Role of Technology

Artificial intelligence (AI) and machine learning (ML): AI and ML can detect and prevent cyberattacks in real-time. For example, AI-powered systems can analyze network traffic to identify suspicious patterns that may indicate an attack.
Blockchain: Blockchain can be used to create secure and tamper-proof records of transactions. This can help protect financial institutions from fraud and other financial crimes.
Encryption: Encryption can be used to protect sensitive data from unauthorized access. This includes data on servers and devices, as well as data that is transmitted over the network.
Multi-factor authentication (MFA): MFA adds an extra layer of security to logins by requiring users to provide two or more levels of authentication, such as a password and a one-time code. This can help to prevent unauthorized access to accounts, even if an attacker has compromised a user’s password.
Zero-trust security: The zero-trust security model trusts no user or device. This model requires all users and devices to be authenticated and authorized before accessing resources.
Security information and event management (SIEM): SIEM systems collect and analyze security logs from across an organization to identify suspicious activity.
Application security testing (AST): AST tools are used to identify and fix security vulnerabilities in software applications.
Endpoint detection and response (EDR): EDR solutions provide real-time monitoring and protection of endpoint devices, such as laptops and servers.
Behavioral analytics: Behavioral analytics tools monitor user and device behavior to identify anomalies that may indicate an attack.